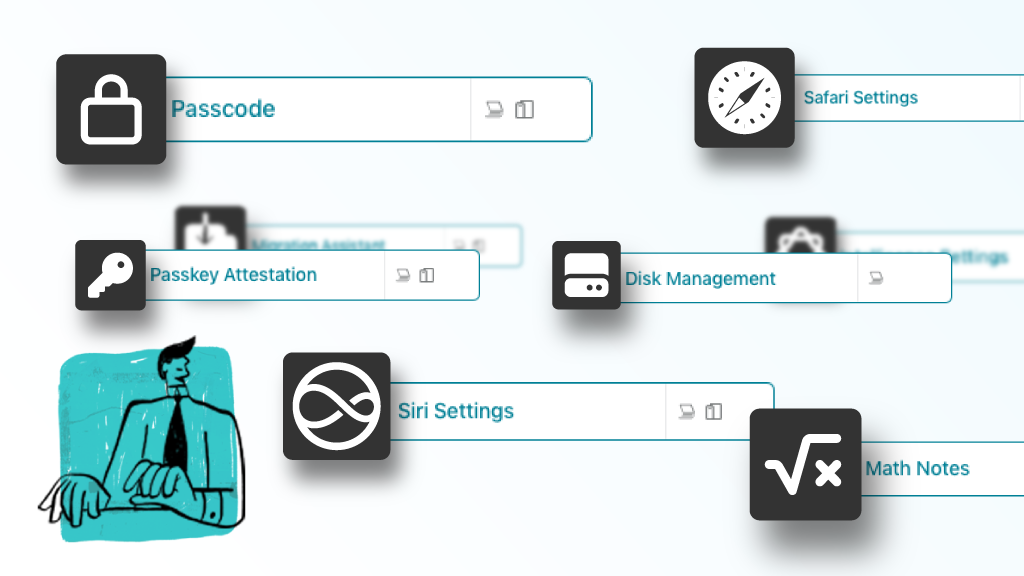
Declaration Configuration Objects
Addigy now supports native Apple Declaration Configuration Objects in OS 26+. Learn what DDM means for IT managers and MSPs managing Apple device fleets.
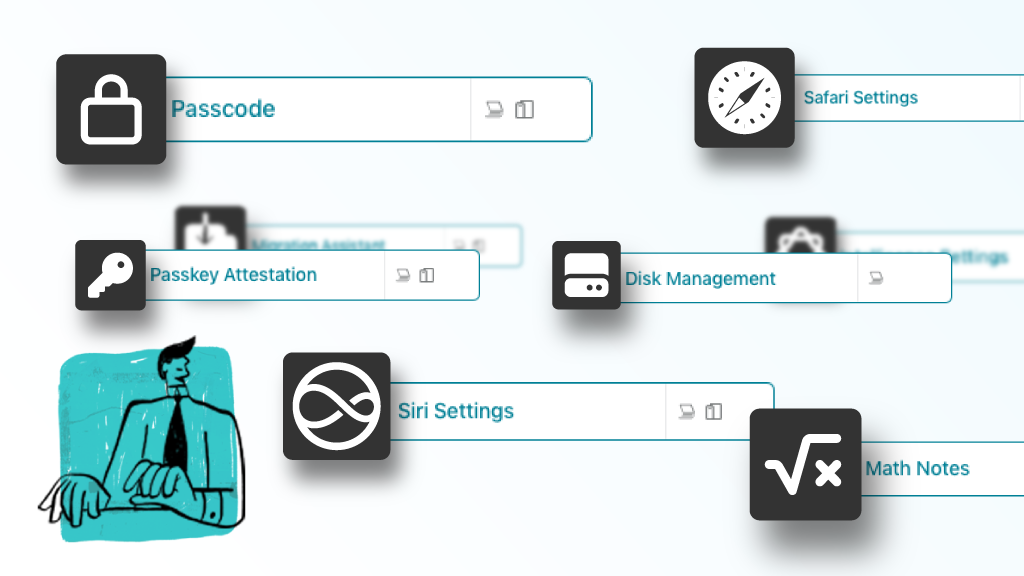
Addigy now supports native Apple Declaration Configuration Objects in OS 26+. Learn what DDM means for IT managers and MSPs managing Apple device fleets.
Join an upcoming webinar to see the features of Addigy and ask questions.
We’ll discuss your specific needs and show you how Addigy can help solve them.